In today’s digital age, businesses face an ever-increasing threat landscape when it comes to IT security. Cyberattacks are becoming more sophisticated and frequent, targeting sensitive data, customer information, and intellectual property. To mitigate these risks, businesses must implement robust IT security solutions. In this article, we will explore 10 essential IT security solutions that every business needs to stay protected.
Table of Contents
Firewall Protection: Safeguarding Your Network with IT Security Solutions

Implementing a firewall solution is crucial for businesses to protect their networks from external threats. By monitoring incoming and outgoing network traffic, firewalls block unauthorized access attempts and potential malware. With robust firewall protection, businesses ensure that only authorized users gain access to sensitive data.
Intrusion Detection and Prevention Systems: Detecting and Blocking Threats Intrusion Detection and Prevention Systems (IDPS) are vital components of any IT security strategy. They actively monitor network traffic, identifying and blocking suspicious activities or potential attacks. With IDPS in place, businesses can detect and respond to threats in real time, preventing unauthorized access and protecting their systems.
Secure Email Gateways: Filtering Out Malicious Emails
Email remains a common vector for cyberattacks. Secure email gateways provide an additional layer of protection by filtering out spam, phishing attempts, and malicious attachments. These IT security solutions scan incoming and outgoing emails, minimizing the risk of employees falling victim to email-based attacks.
Endpoint Protection: Securing Devices and Endpoints
In an era of mobile devices and remote work, securing endpoints is crucial. Endpoint protection solutions encompass antivirus, anti-malware, and encryption tools. They safeguard laptops, desktops, smartphones, and tablets, ensuring devices are protected against malware and unauthorized access.
Data Loss Prevention: Safeguarding Sensitive Information
Data loss prevention (DLP) solutions prevent the unauthorized transmission or exfiltration of sensitive data. These IT security solutions use advanced techniques to identify and protect confidential information, such as personally identifiable information (PII) and trade secrets. Implementing DLP measures mitigates the risk of data breaches and ensures compliance with data protection regulations.
Identity and Access Management: Controlling User Permissions
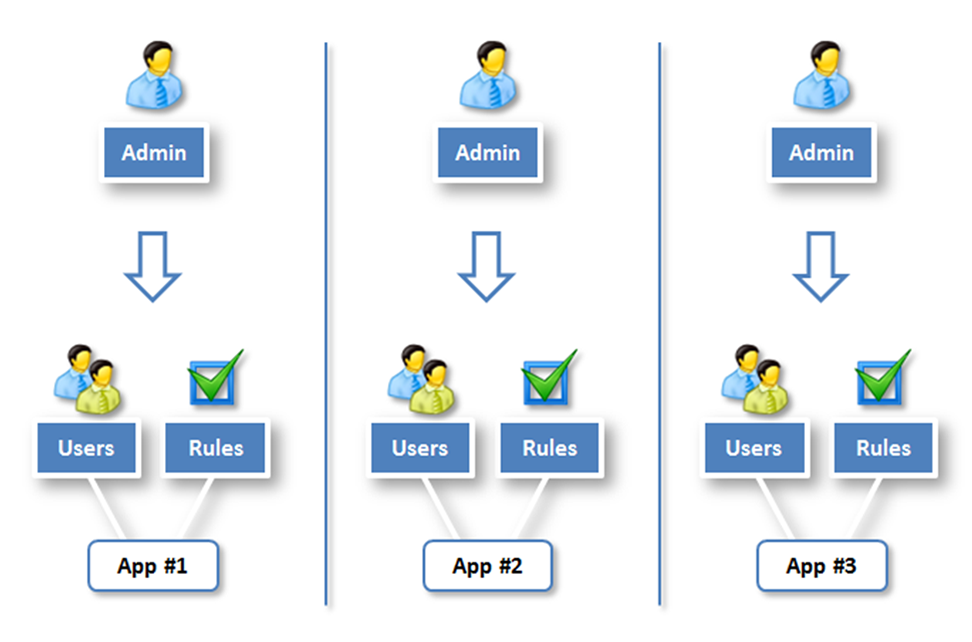
Effective identity and access management (IAM) solutions play a vital role in securing business resources. IAM ensures that only authorized individuals have access to sensitive systems and data. By implementing strong authentication mechanisms, role-based access controls, and privileged access management, businesses minimize the risk of unauthorized access and insider threats.
Security Information and Event Management: Centralized Monitoring and Analysis
Security Information and Event Management (SIEM) solutions provide centralized monitoring and analysis of security events across an organization’s IT infrastructure. By aggregating logs from various systems and applications, SIEM solutions detect and respond to security incidents in real-time, enhancing the organization’s overall security posture.
Vulnerability Management: Identifying and Patching Weaknesses
IT environments are often exposed to vulnerabilities that cybercriminals can exploit. Vulnerability management solutions help businesses identify and prioritize vulnerabilities in their systems, applications, and network infrastructure. Promptly patching these weaknesses minimizes the risk of exploitation and maintains a secure environment.
Backup and Disaster Recovery: Preparedness for the Unexpected
Backup and disaster recovery solutions are essential for business continuity. They ensure that critical data and systems can be restored in the event of a cyberattack, natural disaster, or hardware failure. By regularly backing up data and testing recovery processes, businesses minimize downtime and mitigate the impact of potential incidents.
Employee Security Awareness Training: Strengthening the Human Firewall

No IT security solution is complete without addressing the human element. Employees play a crucial role in maintaining a secure environment. Comprehensive security awareness training educates employees about IT security solutions, potential threats, and best practices. By strengthening the human firewall, businesses significantly reduce the risk of successful cyberattacks.
Conclusion:
In today’s digital landscape, businesses must prioritize IT security solutions to protect their valuable assets from cyber threats. Implementing essential security measures such as firewall protection, intrusion detection and prevention systems, secure email gateways, endpoint protection, data loss prevention, identity and access management, security information and event management, vulnerability management, backup and disaster recovery, and employee security awareness training is crucial for maintaining a secure environment. By investing in these IT security solutions, businesses can stay one step ahead of cybercriminals and ensure the safety of their data and operations.
Learn about: Unleash the Power of the Metamorphic Virus: Revolutionizing Cyber Threats with the Next Generation of Malware