As technology continues to advance, so do the techniques used by cybercriminals. Malware is one of the most common forms of cyber attacks, and its evolution has led to the emergence of new forms of malware such as metamorphic viruses. In this article, we will delve into the world of metamorphic viruses and understand how they are different from traditional viruses. We will also explore their characteristics, their impact on the security industry, and how they can be prevented.
Table of Contents
What are metamorphic-viruses?
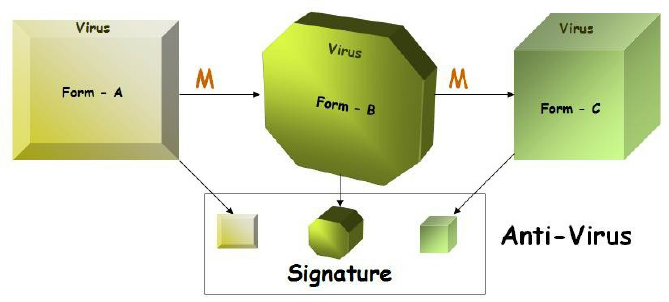
A metamorphic virus is a type of malicious software that is designed to mutate and change its code continuously to evade detection by antivirus software. This makes it difficult for security experts to identify and eradicate the virus. Unlike traditional viruses that remain static in their code, metamorphic viruses can create new variants of themselves that have different signatures and behavior patterns. This means that even if one variant is detected and removed, there is a high probability that another variant may still exist undetected. Metamorphic viruses are highly sophisticated and can self-modify their code, making them challenging to detect and eliminate.
Characteristics of metamorphic-viruses
Metamorphic viruses have several characteristics that set them apart from traditional viruses. Firstly, they have the ability to change their code and structure to create new variants that are different from the original. Secondly, they can generate random instructions to avoid detection by antivirus software. Thirdly, they can encrypt their code, making it difficult for antivirus software to identify the virus. Fourthly, they can use polymorphism, which is a technique that allows the virus to create different code sequences that have the same functionality. Lastly, they can change their execution patterns, making it challenging to analyze and detect their behavior.
How metamorphic-viruses evade detection
Metamorphic viruses evade detection by antivirus software by continuously changing their code and structure. This makes it challenging for antivirus software to identify the virus since it does not have a static signature. Additionally, metamorphic viruses can use anti-emulation techniques to prevent detection by security software that analyzes the virus’s behavior. For example, the virus can create an endless loop that confuses the emulator and prevents it from detecting the virus. Another technique used by metamorphic viruses is the use of garbage instructions, which are instructions that have no effect on the virus’s behavior but are used to confuse the emulator.
Impact of metamorphic-viruses on the security industry
The emergence of metamorphic viruses has had a significant impact on the security industry. Traditional antivirus software that relies on signature-based detection is no longer sufficient in detecting metamorphic viruses. This has led to the development of new security technologies such as behavior-based detection, which analyzes the behavior of the virus instead of its signature. Additionally, security experts have developed sandboxing technology that runs potentially malicious code in a virtual environment to prevent it from infecting the host system. The emergence of metamorphic viruses has also led to an increase in cybersecurity research and development, with security experts continuously exploring new techniques to detect and eliminate metamorphic viruses.
Prevention of metamorphic-viruses
Preventing metamorphic viruses requires a multi-layered approach to cybersecurity. Firstly, it is essential to use antivirus software that has behavior-based detection capabilities. This type of software can detect the virus’s behavior patterns even if it mutates its code. Secondly, it is essential to keep software and operating systems up-to-date with the latest security patches to prevent the exploitation of vulnerabilities by the virus. Thirdly, it is important to educate users on safe internet practices, such as not clicking on suspicious links or downloading attachments from unknown sources. Users should also be trained to identify and report suspicious emails or messages that may contain malware.
Additionally, organizations should implement strict security policies that limit the use of external devices and restrict access to sensitive information. Finally, organizations should conduct regular security audits and penetration testing to identify vulnerabilities and ensure that their security measures are effective.
Examples of metamorphic-viruses
There are several examples of metamorphic viruses that have caused significant damage in the past. One such example is the Metamorphic Engine, which is a toolkit used to create metamorphic viruses. The Metamorphic Engine is highly customizable and can generate unique variants of viruses with each infection. Another example is the W32.Mutant, which is a metamorphic virus that was first discovered in 2003. The W32.Mutant uses advanced encryption techniques and anti-emulation techniques to evade detection by antivirus software. The virus also uses polymorphism to create multiple variants of itself that are difficult to identify.
Future of metamorphic viruses
As technology continues to evolve, it is likely that metamorphic viruses will become even more sophisticated and challenging to detect. Security experts predict that future metamorphic viruses will be capable of using artificial intelligence and machine learning techniques to evolve and adapt their behavior.
Additionally, they may use advanced encryption techniques that make it almost impossible to detect the virus. To combat these threats, security experts are developing new techniques such as genetic algorithms, which can detect and eliminate unknown viruses. However, as metamorphic viruses become more complex, it is likely that the battle between cybersecurity experts and cybercriminals will continue.
Conclusion
Metamorphic viruses are a new generation of malware that are highly sophisticated and challenging to detect. They have several characteristics that set them apart from traditional viruses, and they have had a significant impact on the security industry. To prevent these types of viruses, it is essential to use behavior-based detection software, keep software and operating systems up-to-date, and educate users on safe internet practices. As technology continues to evolve, it is likely that metamorphic viruses will become even more complex, and security experts will need to develop new techniques to combat them.learn about Protect your sensitive data with the power of RC4 encryption online – start safeguarding your information today